Bu yazımda sizlere Azure Bastion’ın kurulumundan ve kullanım amacından bahsedeceğim. Bizlere TLS üzerinden sanal makinelerimize güvenli ve sorunsuz bir şekilde 433 numaralı portu kullanarak RDP/SSH bağlantısı yapmamızı sağlar. Azure Bastion ile bağlantı sağlarken, makineleriniz Public IP (Genel IP) adresine ihtiyaç duymazlar. Dolayısıyla dışardan gelecek tehditlere ve saldırılara karşı korunmuş olurlar.
Azure sanal makinenize RDP/SSH bağlantısı yapabilmek için bir RDP veya SSH istemcisine ihtiyacınız yoktur. Sanal makinenize tarayıcıdan RDP/SSH bağlantısı yapabilmek için Azure portalını kullanabilirsiniz.
Kurulum ve Yapılandırma
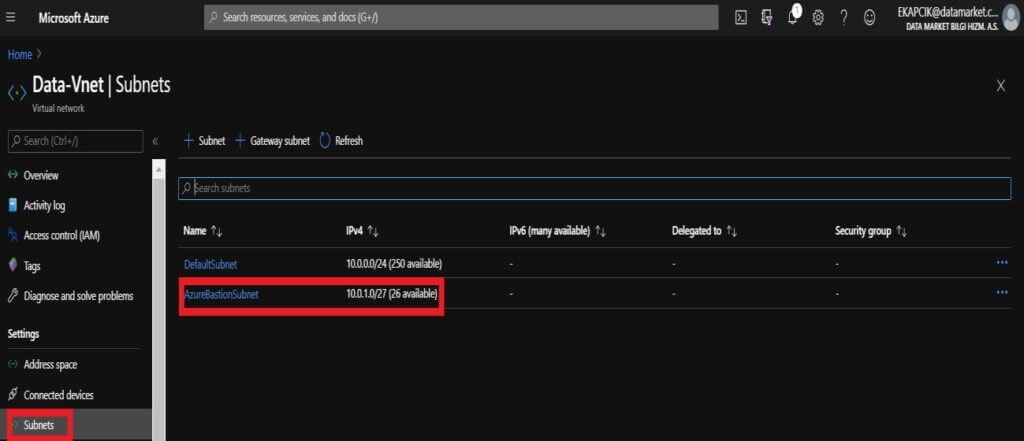
İlk olarak sanal makinemizin sahip olduğu Virtual Network (Sanal Ağ) menüsünden Subnet (Alt ağ) kısmına gidiyoruz. AzureBastionSubnet isminde ve /27 veya daha büyük bir alt ağı kullanmak şartıyla bir alt ağ ekliyoruz. Burada önemli nokta subnet adı AzureBastionSubnet olmak zorundadır.
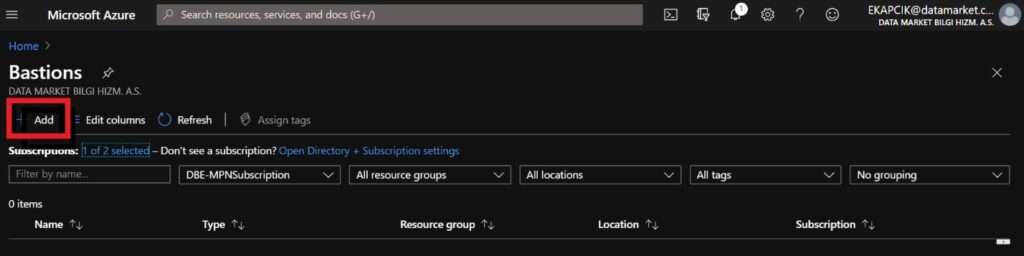
Azure Portal sayfası üzerinden Bastion ekranına geliyoruz ve Add ile devam ediyoruz.
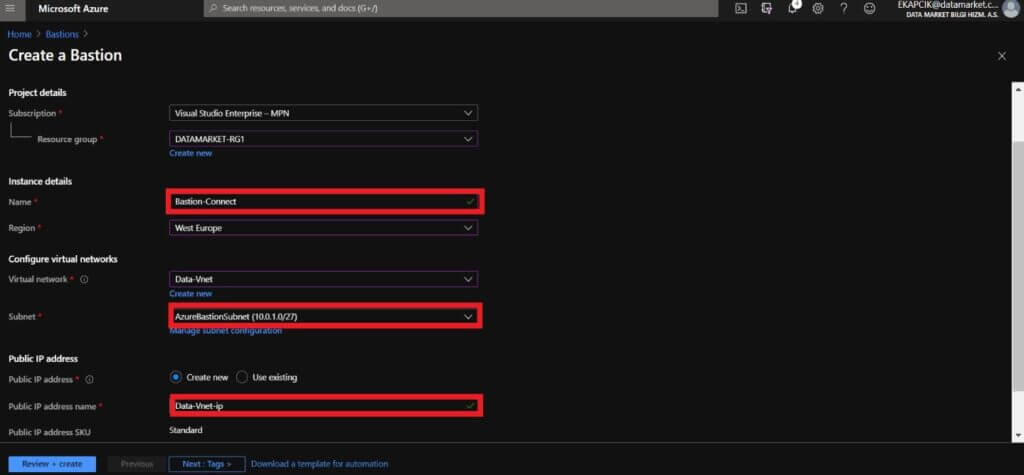
- Name: Azure Bastion’a bir isim veriyoruz.
- Subnet : Bastion’ın dağıtılacağı alt ağı seçiyoruz.. Yani AzureBastionSubnet’ini seçiyoruz.
- Public IP address : Bu, RDP / SSH’ye erişilecek olan Bastion kaynağının genel IP’sidir (443 numaralı bağlantı noktası üzerinden).
Bu işlemleri gerçekleştirdikten sonra Review+Create ile devam ediyoruz ve gelen ekranda Create ile kurulumu tamamlıyoruz.
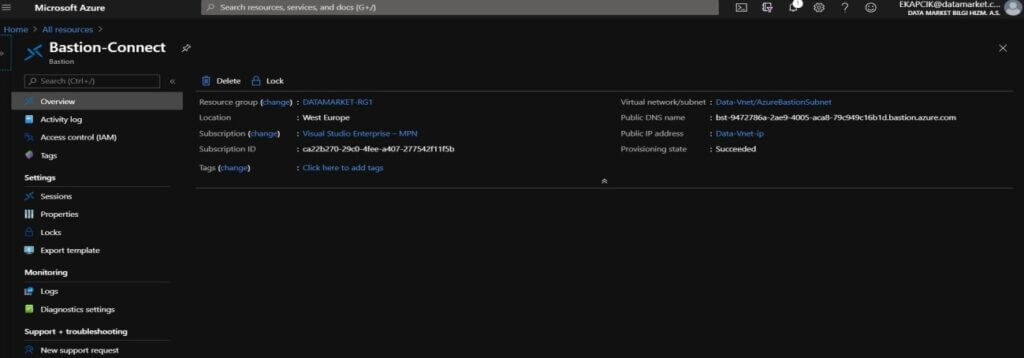
Azure Bastion kurulumunun başarıyla tamamlandığını görüyoruz.
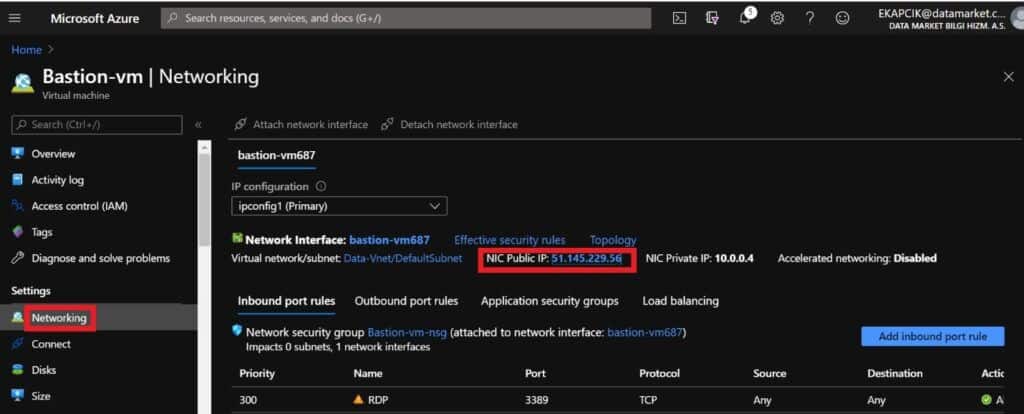
Sanal makinemizin Networking > NIC Public IP kısmına gidiyoruz ve Public IP’mizi kaldırıyoruz.
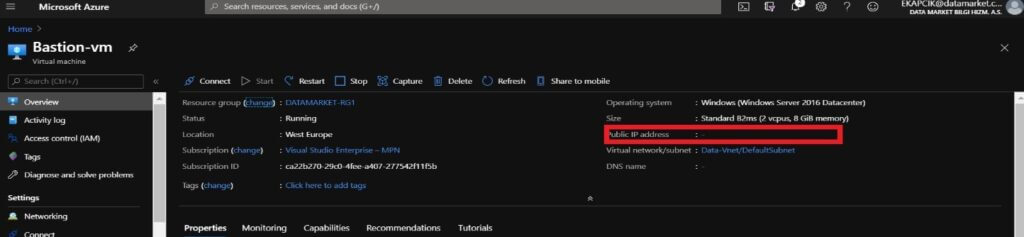
Sanal makine çalışır durumdayken Public IP adresinin olmadığını görebiliyoruz.
Sanal makinemiz üzerinde Connect > Bastion ile kullanıcı bilgilerimizi girerek makinemize bağlanıyoruz.
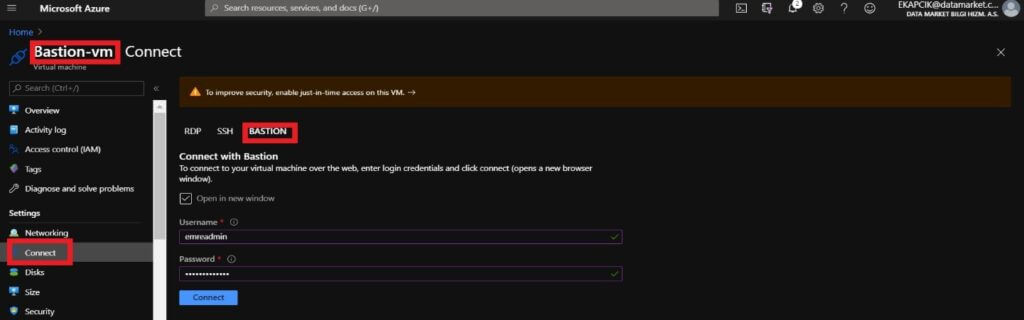
Connect ile ilerliyoruz ve sanal makinemiz yeni bir sekmede açılıyor.
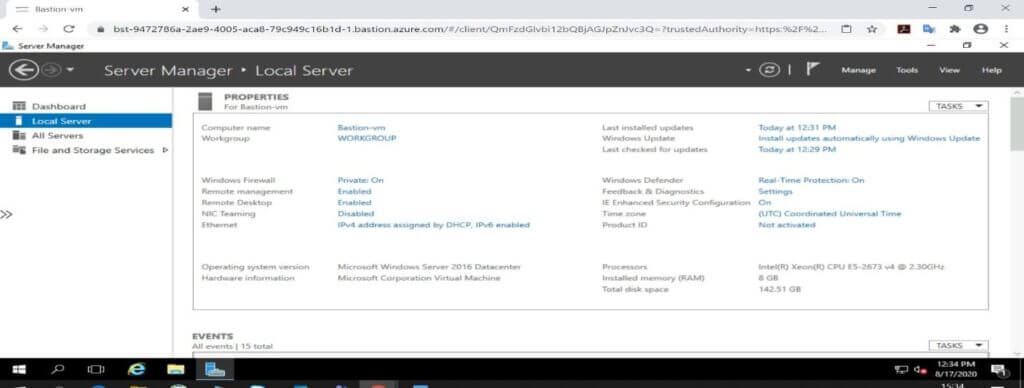
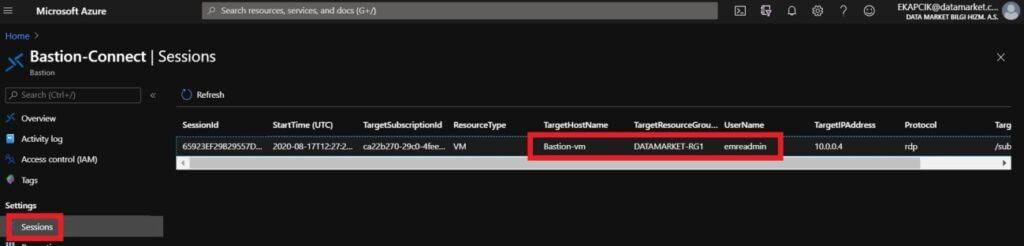
Aynı zamanda Azure Bastion sayfasının altında Session kısmında Bastion ile açılan oturumları görebiliyoruz.
Referanslar:
https://docs.microsoft.com/en-us/azure/bastion/bastion-overview
https://docs.microsoft.com/en-us/azure/bastion/quickstart-host-portal